To connect an Azure MySQL Database, or other services in Azure, one of the most secure methods to do this is with a Private Endpoint. Microsoft document the architecture they recommend using an App Service connecting to a MySQL Server, which is good if you are using the Azure Portal, but there are some missing components if you are using Terraform.
Content
Design
Microsoft do give some more simple method to allow access to the MySQL Server, by whitelisting IP Addresses or allowing Azure Services Access. However, you can only whitelist with confidence if you have a fixed IP range and the allowing all access would open it up to all services within all subscriptions. You can see these methods on the Microsoft Documentation: https://docs.microsoft.com/en-us/azure/mysql/howto-connect-webapp
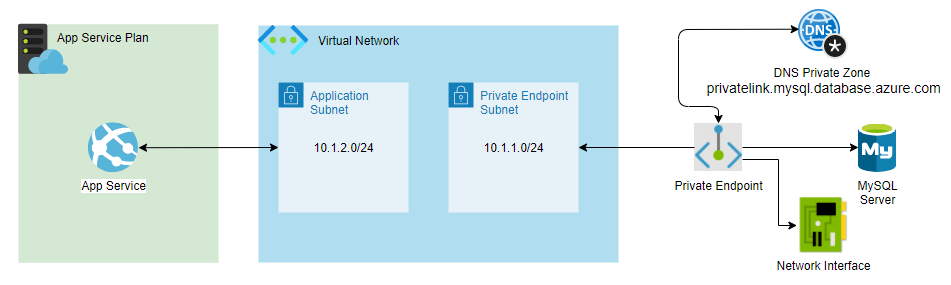
A better method is to lock the server off from the internet and allow access via a Private Endpoint in a Virtual Network. This design is references in the documentation here: https://docs.microsoft.com/en-us/azure/architecture/example-scenario/private-web-app/private-web-app. As you can see it is very simple and have few components, however, when you use the Portal to create these most are dynamically created through simple entries.
I have then depicted the connectivity of these in a slightly different view that shows all the components and how we are going to connection them via Terraform.
Building with Terraform
In each section I will highlight any particular code, but the full example is at the end.
Virtual Network
This is the centre feature to the design that we will create first. You can also create the subnets at this time, but to break it down I am only going to create the VNet itself. With the VNet we are keeping it simple so we are only entering the name and the DNS IP Address, which we will use some hardcoded values that you can always change.
DNS
address_space = ["10.1.0.0/16"]
dns_servers = ["10.0.0.4", "10.0.0.5"]
MySQL Server
You probably can do this in another order, but I followed the same process in creating them in the Portal. Within this I have included dynamically creating the MySQL password. A key part is the ‘mysql_server_sku’ version as this requires to be a General Purpose version or above, which is what I have set the default to. You can also see where I have enforced the firewall to disallow public access with ‘public_network_access_enabled’.
MySQL SKU
variable "mysql_server_sku" {
type = string
description = "MySQL Server SKU"
default = "GP_Gen5_2"
}
Dynamic Password
resource "random_password" "password" {
length = 20
min_upper = 2
min_lower = 2
min_numeric = 2
min_special = 2
}
administrator_login_password = var.mysql_server_password == "" ? random_password.password.result : var.mysql_server_password
MySQL Firewall Settings
variable "mysql_server_settings" {
type = object({
auto_grow_enabled = bool
backup_retention_days = number
geo_redundant_backup_enabled = bool
infrastructure_encryption_enabled = bool
public_network_access_enabled = bool
ssl_enforcement_enabled = bool
ssl_minimal_tls_version_enforced = string
})
description = "MySQL Server Configuration"
default = {
auto_grow_enabled = true
backup_retention_days = 7
geo_redundant_backup_enabled = false
infrastructure_encryption_enabled = false
public_network_access_enabled = false
ssl_enforcement_enabled = true
ssl_minimal_tls_version_enforced = "TLS1_2"
}
}
Subnet
As the subnet will be used more then once, I have made this a custom Module. This can then be called for creating the Private Endpoint subnet and the Applications Subnet. The Private Endpoint Subnet requires there to be no Delegation set, but the Application Subnet does need it. Therefore, I have made that section of the module dynamic. In this example you can also see the subnets I am giving the Private Endpoint and Application.
Delegation
dynamic "delegation" {
for_each = var.subnet_delegation_name == "" ? [] : [1]
content {
name = var.subnet_delegation_name
service_delegation {
name = var.subnet_delegation_type
actions = var.subnet_delegation_actions
}
}
}
Subnets
variable "private_endpoint_subnet" {
type = string
description = "Azure Private Endpoint VNet Subnet Address"
default = "10.1.1.0/24"
}
variable "app_subnet" {
type = string
description = "Azure Application Subnet Address"
default = "10.1.2.0/24"
}
Private Endpoint
As this contains a few components to link everything up, I have also put this into a custom Module. You can see the order of creation below, so you can get an idea of how they are built. I try to keep things dynamic so the connecting of the MySQL Server is part of an array, you can add more resources to this endpoint. Something that caught me out was the DNS Zone name in Terraform. Most every resource that has a ‘name’ can be anything you like within the boundaries of validation as it just gives a title to the resource, but the DNS Zone must be a valid link from the Azure Documentation, which in the Terraform variable below.
Creation Order
- Create Private DNS Zone
- Create Private Endpoint
- Create a Private Endpoint Connection
- Link the DNS Zone to the Virtual Network
Dynamic Resources
private_endpoint_service_connections = [
{
name = "${var.mysql_server_name}.privateEndpoint"
private_connection_resource_id = azurerm_mysql_server.mysql_server.id
subresource_names = ["mysqlServer"]
is_manual_connection = false
}
]
DNS Zone name
variable "dnszone_private_link" {
type = string
description = "Validate Private Link URL https://docs.microsoft.com/en-us/azure/private-link/private-endpoint-dns"
}
resource "azurerm_private_dns_zone" "private-endpoint-dns-private-zone" {
name = var.dnszone_private_link
resource_group_name = var.resource_group_name
}
dnszone_private_link = "privatelink.mysql.database.azure.com"
App Service
We can now add the connecting App Service by creating an App Plan with an App Service connected to a subnet within the same VNet. This has all the standard values and settings, which do not have much requirements to this solution. Two factors that do is the App Plan SKU, which just needs to be Standard or above and the other is the App Settings. Again making thing dynamic, I allow a variable to pass in custom App Settings, but we also need the Subnet settings added. These include the ‘WEBSITE_VNET_ROUTE_ALL’ and the ‘WEBSITE_DNS_SERVER which is set to the Azure DNS IP Address unless you have private DNS Server.
App Settings
locals {
app_settings_subnet = {
WEBSITE_VNET_ROUTE_ALL = 1
WEBSITE_DNS_SERVER = "168.63.129.16"
}
app_settings = merge(var.webapp_app_settings, local.app_settings_subnet)
}
End-to-end Code
You can view the full code on my GitHub Repository PureRandom
These are also two sites where I drew a lot of knowledge from, so I thought they deserved a mention.
If you do find any issues with the code, please message me. This was taken from a larger project so I might have missed one or two things 🙂