Microsoft shifted the Azure Purview to be Tenant aligned, but the AzureRM Provider hasn’t made that move yet, so if you are deploying your Azure infrastructure using Terraform you need to do some alternative changes to get it to work, especially when you’re trying to deploy Purview securely using private networking. After a few painfulContinueContinue reading “Deploying Azure Purview with Terraform: Overcoming AzureRM Limitations”
Tag Archives: Azure
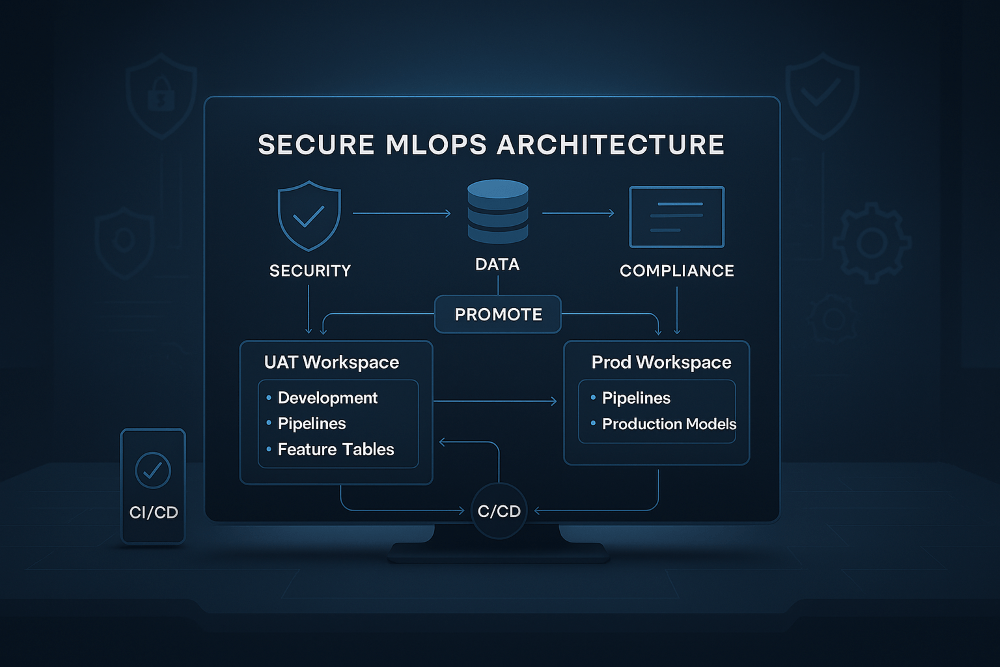
Secure MLOps Design for Databricks and Azure: A Practical Workspace‑Driven Architecture
Most Databricks MLOps guidance assumes you can train and develop directly inside a production Unity Catalog. In many organisations, that’s simply not possible, whether for compliance, data‑security, tenancy boundary or governance reasons. So this post outlines a design concept I created that stays aligned with official Databricks and Azure MLOps guidance while enabling safe, isolated,ContinueContinue reading “Secure MLOps Design for Databricks and Azure: A Practical Workspace‑Driven Architecture”
Bringing AI-Powered Pull Request Reviews to Azure DevOps
AI‑assisted pull request (PR) reviews are quickly becoming standard practice in modern software delivery. GitHub users already benefit from Copilot being deeply embedded into their workflow, offering immediate feedback on code quality, readability, and potential issues at the moment of review. For teams using Azure DevOps, that experience simply doesn’t exist today. There is currentlyContinueContinue reading “Bringing AI-Powered Pull Request Reviews to Azure DevOps”
Choosing the Right Azure DevOps Agent Hosting Strategy in Azure
In the world of continuous integration and continuous delivery (CI/CD), Azure DevOps agents are key resources. These agents are the compute resources that execute your pipeline whether it’s compiling code, running tests, or deploying applications. Without them, your DevOps pipelines are just scripts waiting to be run. Azure DevOps offers two types of agents: Microsoft-hostedContinueContinue reading “Choosing the Right Azure DevOps Agent Hosting Strategy in Azure”
How to Secure Your Terraform State File in Azure
Terraform has become the standard for managing cloud infrastructure, and with good reason. It provides consistent, repeatable deployments and integrates with almost every cloud provider. But there’s one piece that’s often overlooked until it causes problems: the Terraform state file. Your terraform.tfstate file is more than just metadata — it’s the single source of truthContinueContinue reading “How to Secure Your Terraform State File in Azure”
Integrate Azure DevOps Pipelines with Private GitHub Repos
In cloud-native engineering, securely connecting Azure DevOps pipelines to private GitHub repositories is essential — especially when working with Terraform modules that define your infrastructure. This guide walks through how to establish that connection using PowerShell Core, ensuring a secure and maintainable setup. 🛠️ Prerequisites Before you begin, make sure you have: An Azure DevOps organisation andContinueContinue reading “Integrate Azure DevOps Pipelines with Private GitHub Repos”
Managing Azure API Versions Dynamically Using Terraform
When developing APIs for consumption from many callers you can’t just throw in new major or minor updates without impacting how they are calling the API. Doing this can cause major issues so you would normally develop APIs in things like Azure Web Applications with versioning. The callers of the APIs can then reference theseContinueContinue reading “Managing Azure API Versions Dynamically Using Terraform”
Validating Azure APIM in CI: A Practical Approach to Safe API Deployments
When deploying any code you want to validate it as much as you can before deploying. However with APIs in the APIM you can’t validate the XML Policy or the API logic until it is deployed into the API Management Service (APIM). This means you are limited to the options to validate the code, beforeContinueContinue reading “Validating Azure APIM in CI: A Practical Approach to Safe API Deployments”