After you create you Azure MySQL Server, you would like to create a Database, but for security you would like to have a new custom user added with permission. Unfortunately the Azure Providers do not provide this, so we need to use some other skills to get these users in. First we can go aheadContinueContinue reading “Create User on Azure MySQL Database with Terraform”
Category Archives: Cloud
Unable to delete Azure Subnet due to Resources
With Azure Subnets there is an order to deleting the resources. You must disconnect the Virtual Network Subnets before deleting the resources, or you can’t delete the Subnet. This caused myself some issue, while using Terraform as I kicked a Destroy command and did it in the wrong order. However, I found a method onContinueContinue reading “Unable to delete Azure Subnet due to Resources”
Auto Purge Azure Container Registry Images
When adding images into the Azure Container Registry you might start getting a backlog of images that need to be cleaned down. Azure CLI has some features, but you might want more… With the Azure CLI you can use the ‘ACR’ commands, which contain the option of ‘purge’. This can be combined with a tagContinueContinue reading “Auto Purge Azure Container Registry Images”
Automate Security for Azure Container Registry
From March 2021 Azure is deprecating the Container Setting in Azure Web Apps, which changes you to use the new Development Center. This look very nice, but there is a change that is going to force you to have weaker security. This change is to have the Admin Credentials enabled, but there is something youContinueContinue reading “Automate Security for Azure Container Registry”
Testing Azure DevOps Pipelines Locally
I have tried and tried before, plus also read a lot of other people asking for the ability to test Azure YAML Pipelines locally. Now although it is not perfect and some room for improvement, Microsoft has create a way to test your pipeline with some local testing and remote testing without having to checkContinueContinue reading “Testing Azure DevOps Pipelines Locally”
Create Identity in Google Cloud Platform and GSuite
Compare to some other cloud providers, creating an identity via code in GCP is a little fragmented if your using GSuite for your identity storage. The Google Cloud Platform holds your users identity reference and permission, while the other system GSuite hold the security of the users authentication. This can also make the documentation feelContinueContinue reading “Create Identity in Google Cloud Platform and GSuite”
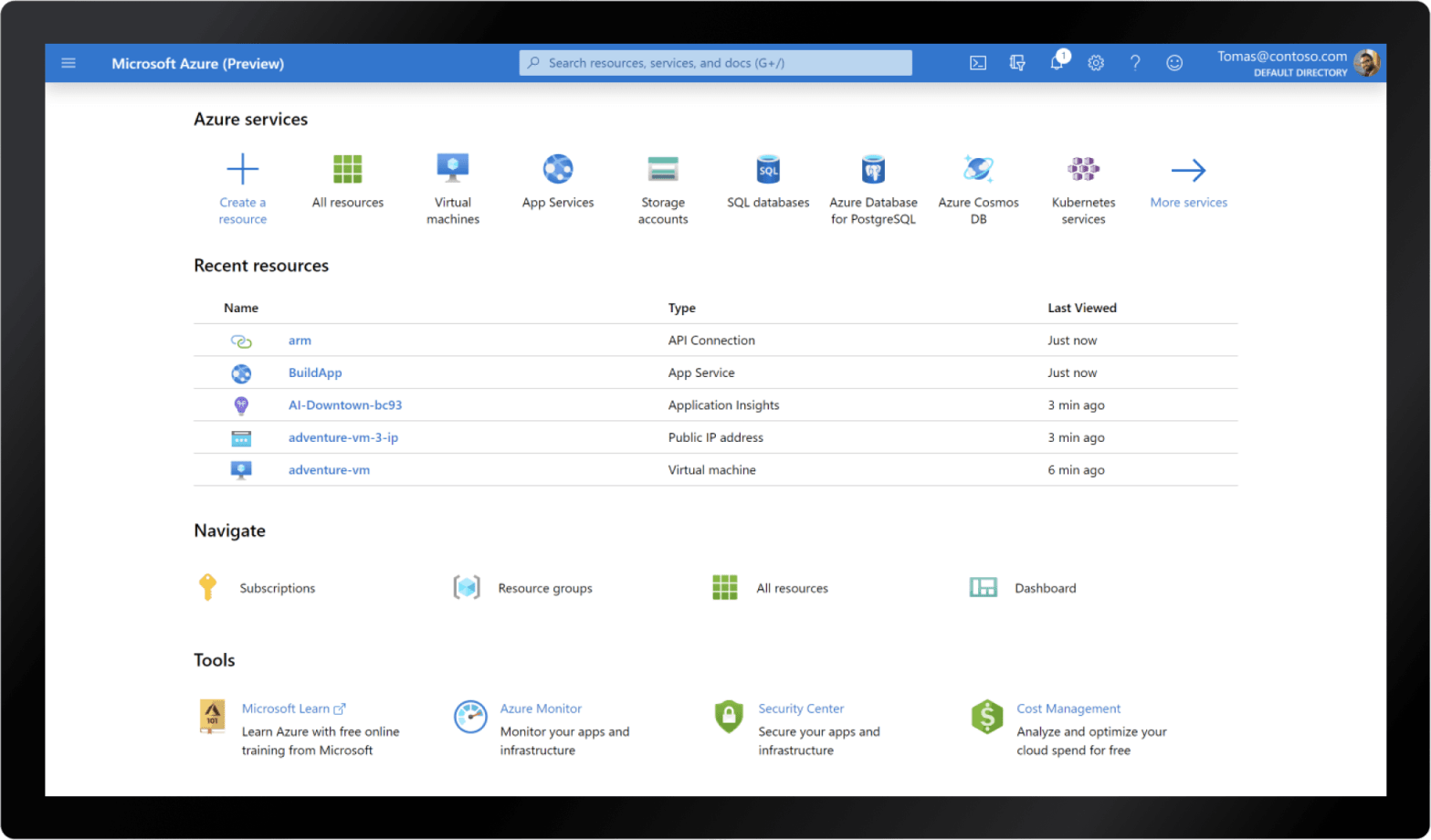
Where to find Azure Tenant ID in Azure Portal?
Some of the documentation about Azure from Microsoft can be confusing and missing, including one I get ask ‘Where is the Tenant ID’. Below I give 3 locations, which there is probably, on where to find the Tenant ID in the portal. I have also added how to get the Tenant ID with the Azure CLI.
Deleting Recovery Service Vault Backup Server (MABS)
This is one of them quick shares to try help the world of Azure developers just a little bit. While doing some Azure Development using the Microsoft Azure REST API, I got to a point to working in the Azure Recovery Service Vault. I was trying to delete a Back Up Server Agent using theContinueContinue reading “Deleting Recovery Service Vault Backup Server (MABS)”